LDAP Injection : TryHackMe Walkthrough
Introduction LDAP, which stands for Lightweight Directory Access Protocol, is
Ciphers Security, are here to provide you with the latest information and trends in the cybersecurity field.
Introduction LDAP, which stands for Lightweight Directory Access Protocol, is
In this ever-changing sphere of cyber security, it becomes utmost
As the cyber world is emerging in today’s time, everyone

NetworkMiner is an open-source traffic sniffer, pcap handler and protocol analyser. Developed

Hi, reader Lucifer here with the new article on information
Hello, guys lucifer here, and in this article, we will
Hello reader, this article is dedicated to discussing how you
Introduction LDAP, which stands for Lightweight Directory Access Protocol, is
In this ever-changing sphere of cyber security, it becomes utmost
As the cyber world is emerging in today’s time, everyone

Conflicts have crossed the physical boundaries and entered the vast, interconnected realm of cyberspace in the digital
The environment of cyber threats is always changing, therefore defense

One of the most important tools that any cybersecurity expert
In the ever-evolving landscape of cybersecurity, understanding and securing network

You can greatly improve your practice sessions if you study
Generating word list from target website using CeWL Custom wordlist
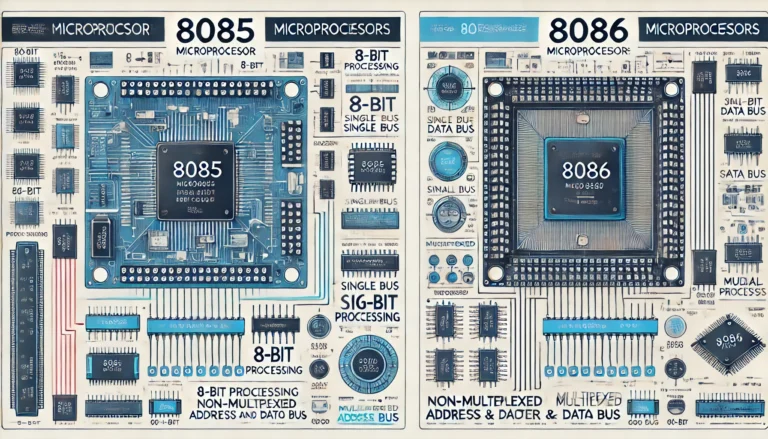
Although Intel produced both the 8085 and 8086 microprocessors, their
An unknown attacker is brute-forcing Linux SSH servers to install
ACL or access control lists are the set of rules
Generating word list from target website using CeWL Custom wordlist
Hello everyone today in this article we are going to
Hello everyone today in this article we are going to