Tools
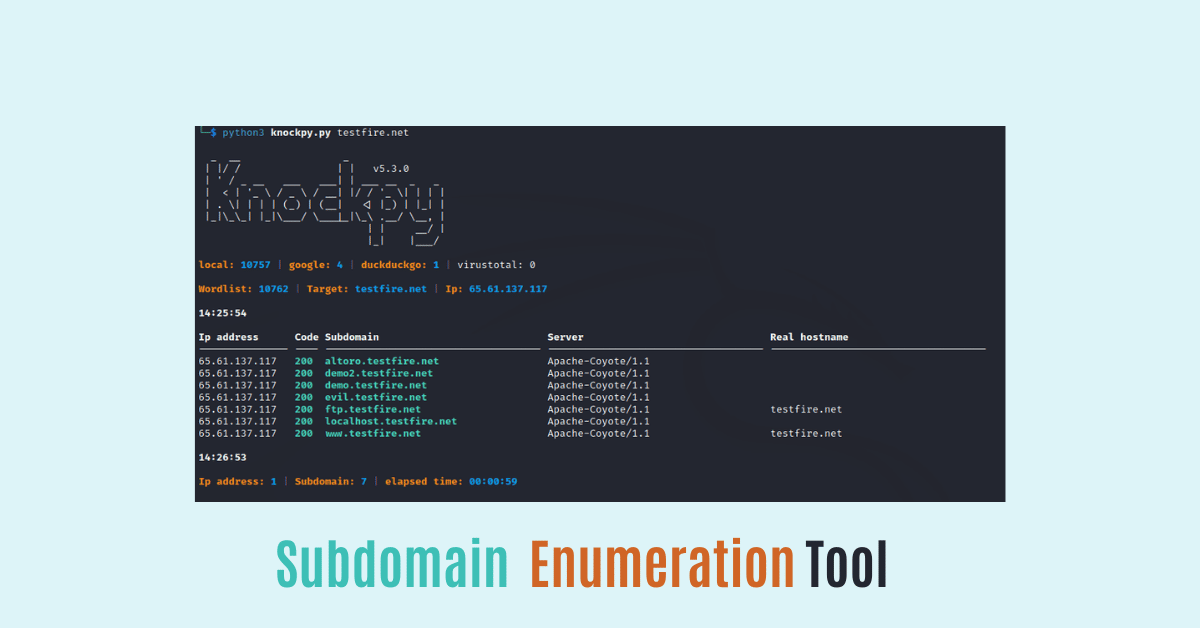
How to install knockpy on Linux for information gathering
- by Team Ciphers Security
- December 13, 2022
- 1 Comment
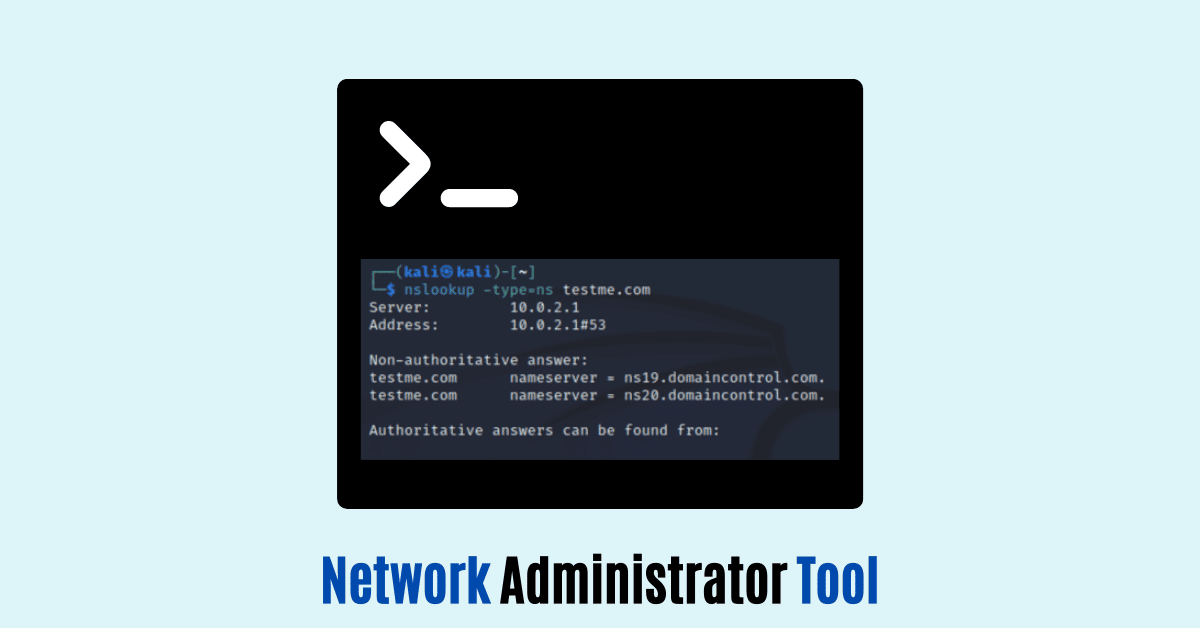
Information Gathering
What is Information Gathering
- by Team Ciphers Security
- December 9, 2022
- 2 Comments
Programming
Introduction to PHP Programming language
- by Team Ciphers Security
- December 8, 2022
- 0 Comments
Programming
Introduction to Python programming language
- by Team Ciphers Security
- December 7, 2022
- 0 Comments
Programming
Introduction to C language with its basic concept
- by Team Ciphers Security
- December 6, 2022
- 0 Comments