Information Gathering
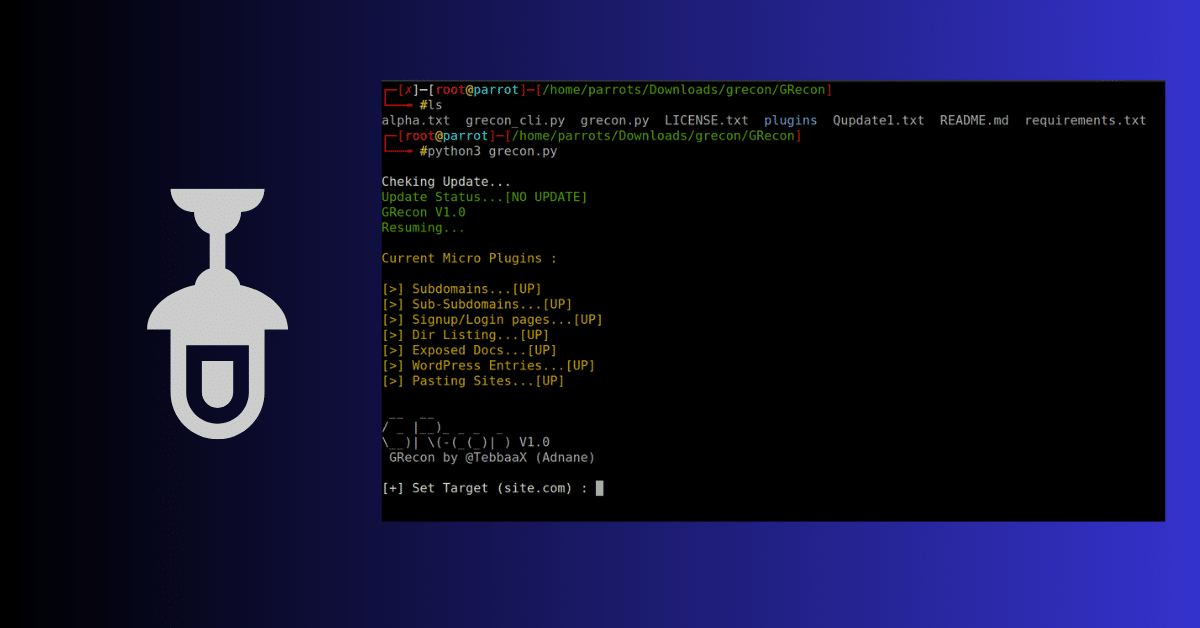
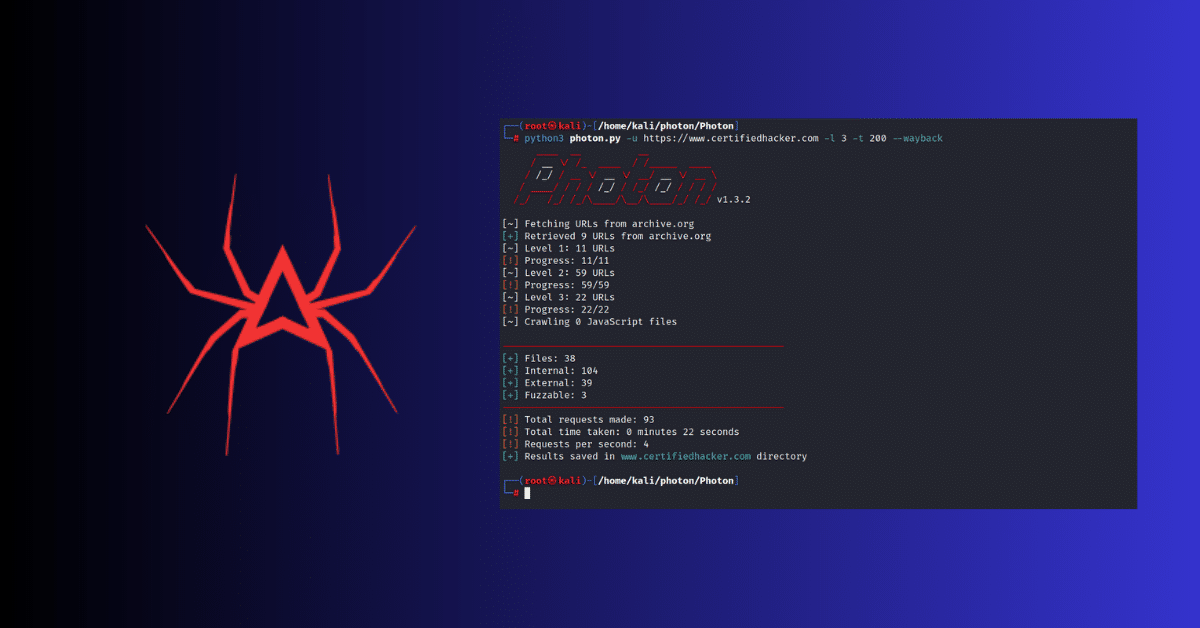
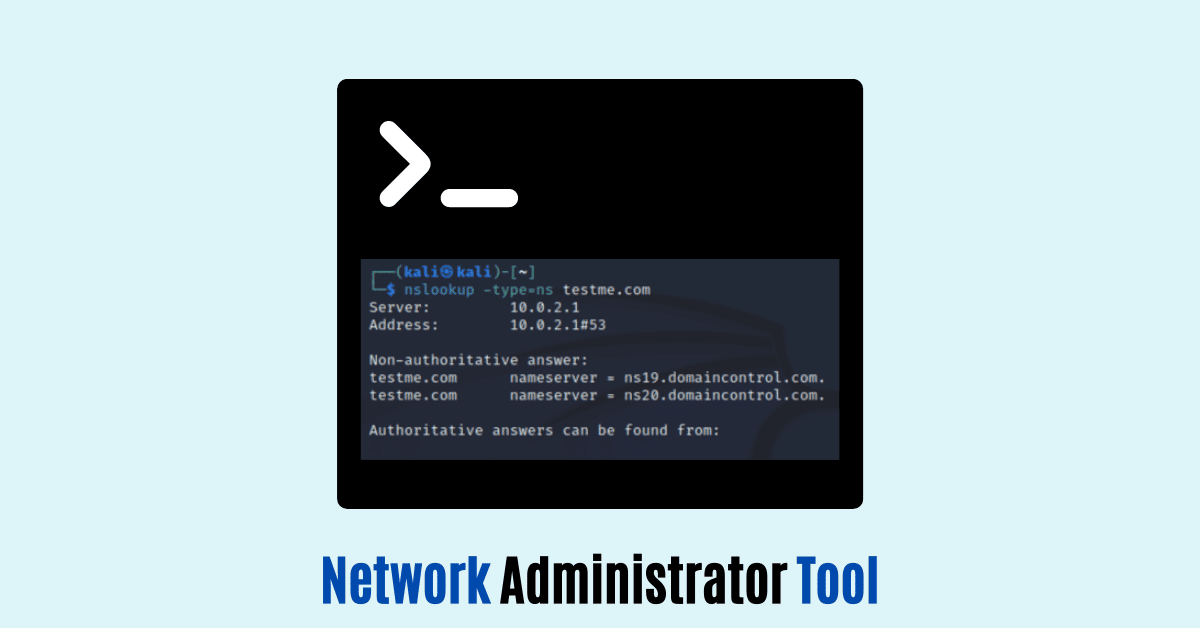
Tools
Best Information Gathering Tools
- by Team Ciphers Security
- December 13, 2022
- 1 Comment
Information Gathering
What is Information Gathering
- by Team Ciphers Security
- December 9, 2022
- 2 Comments