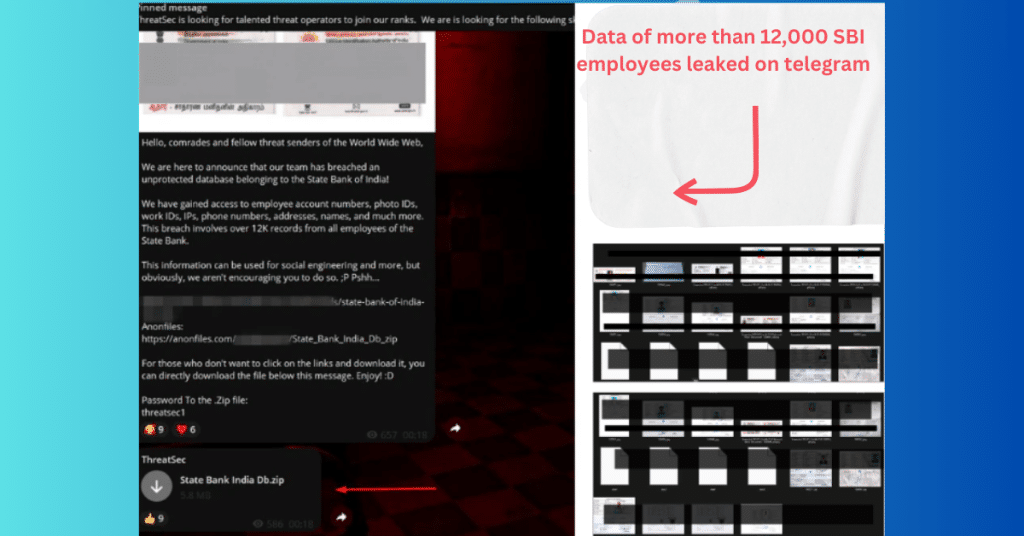
Recently the news has come to know that data of more than 12,000 SBI employees and account holders have leaked through telegram channels which shows that the bank has missed some red flags regarding the attack on the database.
Confidential/sensitive information like a copy of a passbook, Aadhaar card, and voter I’d be leaked. All these data are stored unencrypted which is the biggest mistake of banks and leads to these huge damage to data leakage. Bank will ensure that the hackers/attackers should not be successful even if the data is stolen. And it only happens when all the data stored is encrypted.
Last Friday, on telegram a message from an unknown account with 608 followers come that released a file that contains the account numbers, photo IDs, work IDs, IPs, phone numbers, addresses, names, and a number of other personal details of SBI employees and other customers.
The attacker exploits an unprotected database in which no restrictions are available to access the customer’s financial details like bank balance and recent transactions.
The attacker also leaked more than 4000 employee data like SBI accounts screenshots, Aadhaar cards, and PAN cards openly on a public website which can cause financial damage to those employees and customers.
// 01 Expert’s thoughts related to the SBI data leak
The cyber security expert, Saumay Srivastava disclose the huge SBI data leak through his efforts towards dark web monitoring. According to him, an attacker attacks the infrastructure by exploiting any active vulnerability by using Ransomware as a service (RaaS) attack to attack active infrastructure.
He also says that still, the banking sector is under the target of attackers which leads to huge/massive damage to confidential/sensitive data of employees and account holders or the bank’s reputation.
He highlights the point that with the help of leaked data, an attacker can access the bank accounts of those clients and employees, can conduct transactions and due to weak security these files are easily accessible for them.
// 02 How SBI and other banks prevent their database from such attacks
- Use firewalls, IP-based restrictions, and passwords for authentication.
- Encrypt all confidential and sensitive information like employee IDs, passwords, email addresses, contact numbers, etc.
- Apply active vulnerability scanners for database and cloud storage that scans all loopholes on time.
- Regularly take backup of all sensitive data to prevent data in case of any attack occur.
- Always follow vulnerability management guidelines by CERT-IN.
- Update the security of the database regularly to prevent it from attacks.
- Hide the confidential data of employees and account holders using the robots.txt file, which only can be accessed in the root-level directory.
