Tools
here we will see how to install different types of tools
Tools
Short Report on password attack tools hydra and crunch
- by Team Ciphers Security
- January 15, 2023
- 0 Comments
Tools
Blog
How to use NMAP for penetration testing
- by Team Ciphers Security
- December 21, 2022
- 0 Comments
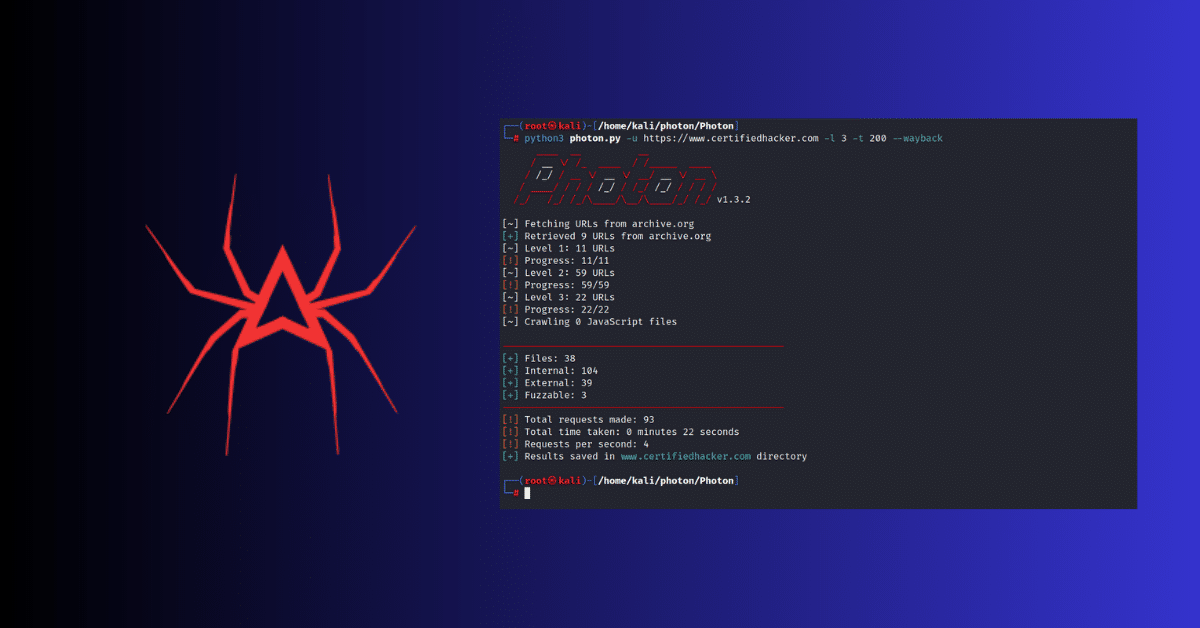
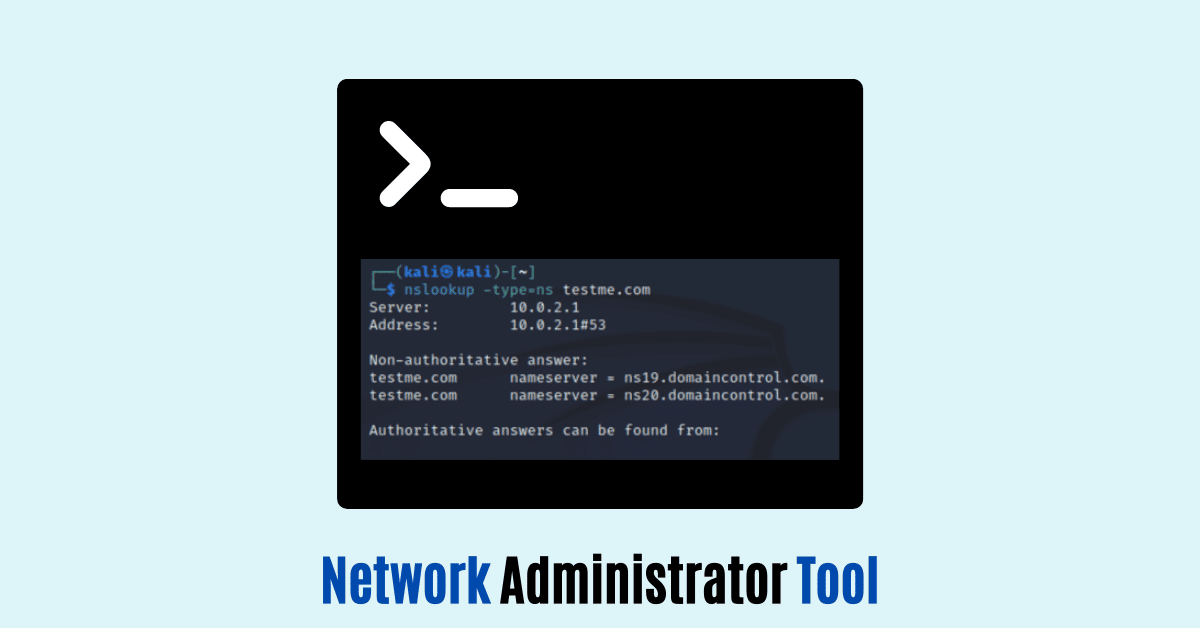
Information Gathering
Tools
Best Information Gathering Tools
- by Team Ciphers Security
- December 13, 2022
- 1 Comment