This room introduces the user to a few protocols commonly used, such as:
- HTTP
- FTP
- POP3
- SMTP
- IMAP
Room Link: Protocols and Servers
Each task about each protocol will be designed to help us understand what happens on the low level and is usually hidden by an elegant GUI (Graphical User Interface).
We will “talk” using the above protocols using a simple Telnet client to fully understand what your GUI client is doing under the hood. Our purpose is not to memorize the protocol commands but rather to get a closer look at the protocol while it is working.
We also discuss some of the insecurities. In particular, we focus on passwords sent in cleartext.
// 01 Task 2 Telnet Protocols
Question: To which port will the telnet command with the default parameters try to connect?
Answer: 23
// 02 Task 3 Hypertext Transfer Protocol (HTTP) Protocols
Question: Launch the attached VM. From the AttackBox terminal, connect using Telnet to 10.10.197.110 80 and retrieve the file flag.thm. What does it contain?
Steps:-
- Launch the VM
- open the terminal and use telnet to browse the flag upon web service at port 80
- telnet 10.10.197.110 80
- GET /flag.thm HTTP/1.1
host: telnet - you’ll get the flag
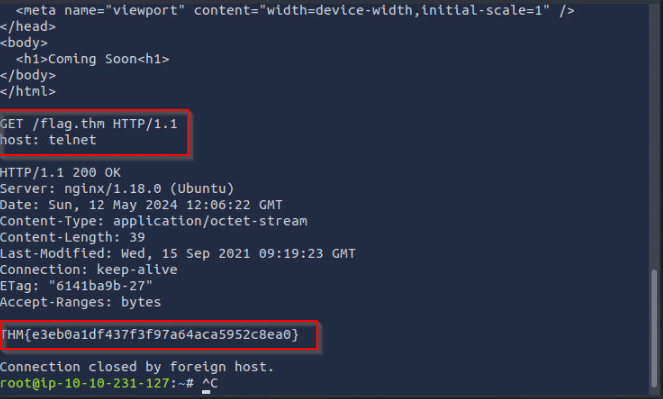
Answer: THM{e3eb0a1df437f3f97a64aca5952c8ea0}
// 03 Task 4 File Transfer Protocol (FTP) Protocols
Question: Using an FTP client, connect to the VM and try to recover the flag file. What is the flag?
- Username: frank
- Password: D2xc9CgD
- create the FTP connection with the following credentials
- ftp 10.10.197.110
- provide the username and password
- now use ls command for listing the content
- you’ll see the flag file, now you need to read it, for reading you need to download it to your local system
- for downloading the file, use get command { get ftp_flag.thm }
- after that, open another terminal and read the file with cat command
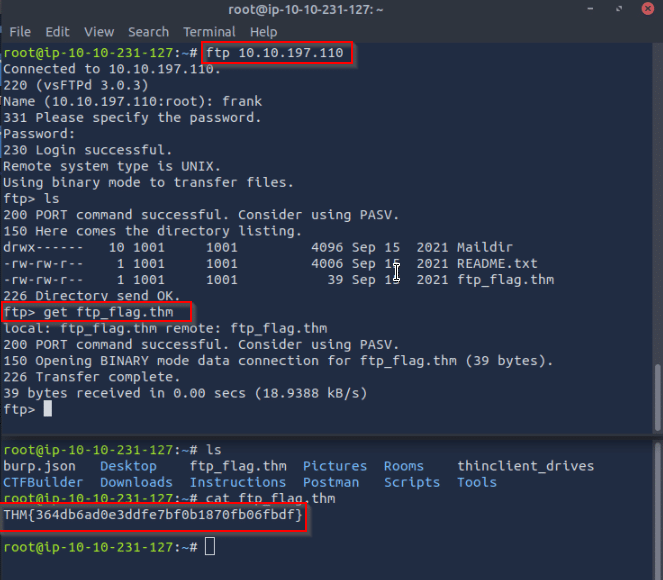
Answer: THM{364db6ad0e3ddfe7bf0b1870fb06fbdf}
// 04 Task 5 Simple Mail Transfer Protocol (SMTP) Protocols
Question: Using the AttackBox terminal, connect to the SMTP port of the target VM. What is the flag that you can get?
Hint: Connect the telnet using port 25, telnet 10.10.197.110 25
Answer: THM{5b31ddfc0c11d81eba776e983c35e9b5}
// 05 Task 6 Post Office Protocol 3 (POP3)
Question: Connect to the VM (10.10.197.110) at the POP3 port. Authenticate using the username frank and password D2xc9CgD. What is the response you get to STAT?
- connect the POP3 using telnet at port 110
- provide username and password
- USER frank
- PASS D2xc9CgD
- for 1 question, use the command STAT
- For 2 questions, use the command LIST
Answer: +OK 0 0
Question: How many email messages are available to download via POP3 on 10.10.197.110?
Answer: 0
// 06 Task 7 Internet Message Access Protocol (IMAP)
Question: What is the default port used by IMAP?
Answer: 143
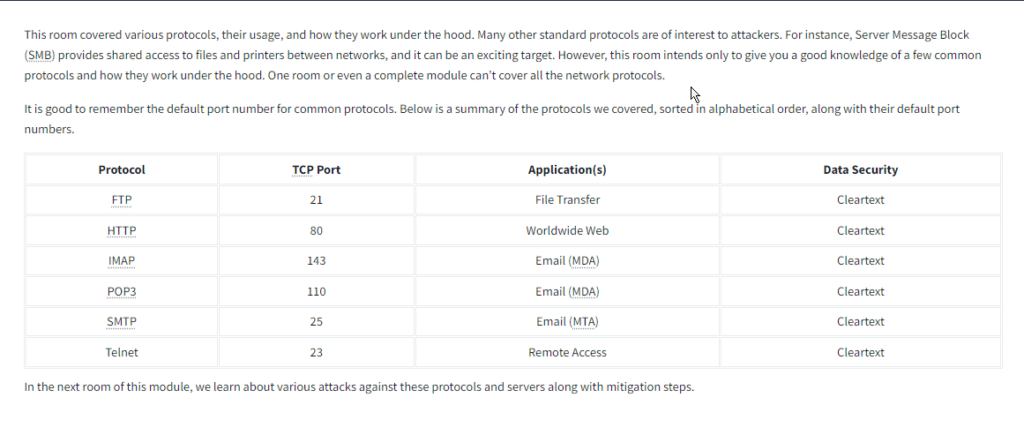
// 07 Task 8 Summary