OSINT is short for open-source intelligence framework that focuses on gathering information about the target available over the internet.
This framework helps security researchers for performing automated footprinting and reconnaissance, OSINT research, and intelligence gathering.
OSINT framework focuses on gathering information from free tools and resources. Still, some sites included might require registration or offer more data in exchange for money, but OSINT will provide at least a portion of the available information for no cost.
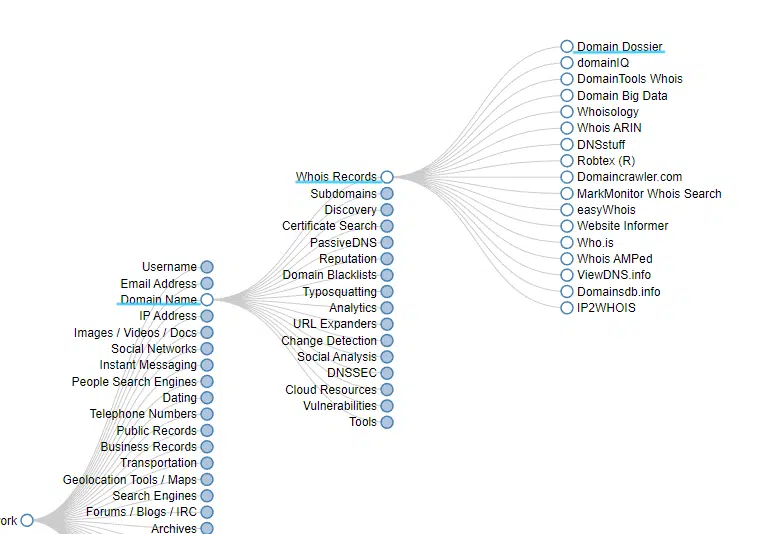
This framework has a simple web interface that contains the list of OSINT tools arranged in a category with a tree structure on the web interface
// 01 Indicators in the OSINT Framework
- (T) – Indicates a link to a tool that must be installed and run locally
- (D) – Google Dork, for more information: click here
- (R) – Requires registration
- (M) – indicates a URL that contains the search term and the URL itself must be edited manually
// 02 how to use this framework
1. Open any browser and search for the OSINT framework website.
2. It will appear as shown in the screenshot below
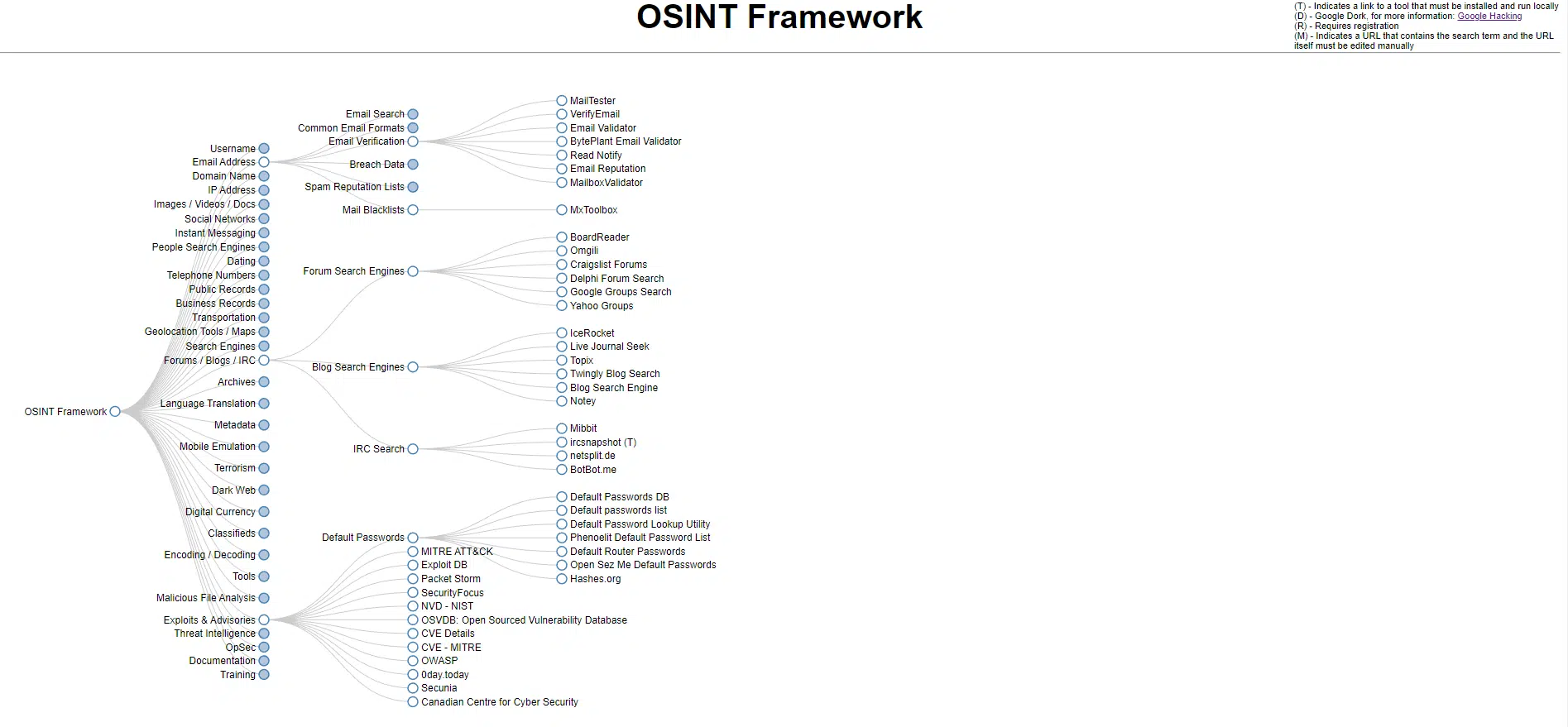
3. This is the tree-structured classified list of all the tools available for Open-source intelligence reconnaissance
4. When you click on any categories in the list then it will show many useful resources in the form of a subtree on the screen.
5. Let’s take a person as our target, and we need to gather information about that person with his/her name. then we will click on the username category and then there will be two subcategories that are a username search engine and specific sites.
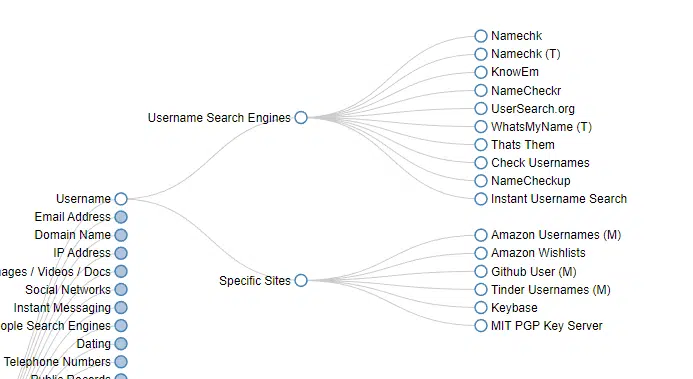
6. Now if you want to search for that username in specific website data then click on specific sites and choose your tool to use, but for my I will search him on the internet with every website then I will go for the username search engine category.
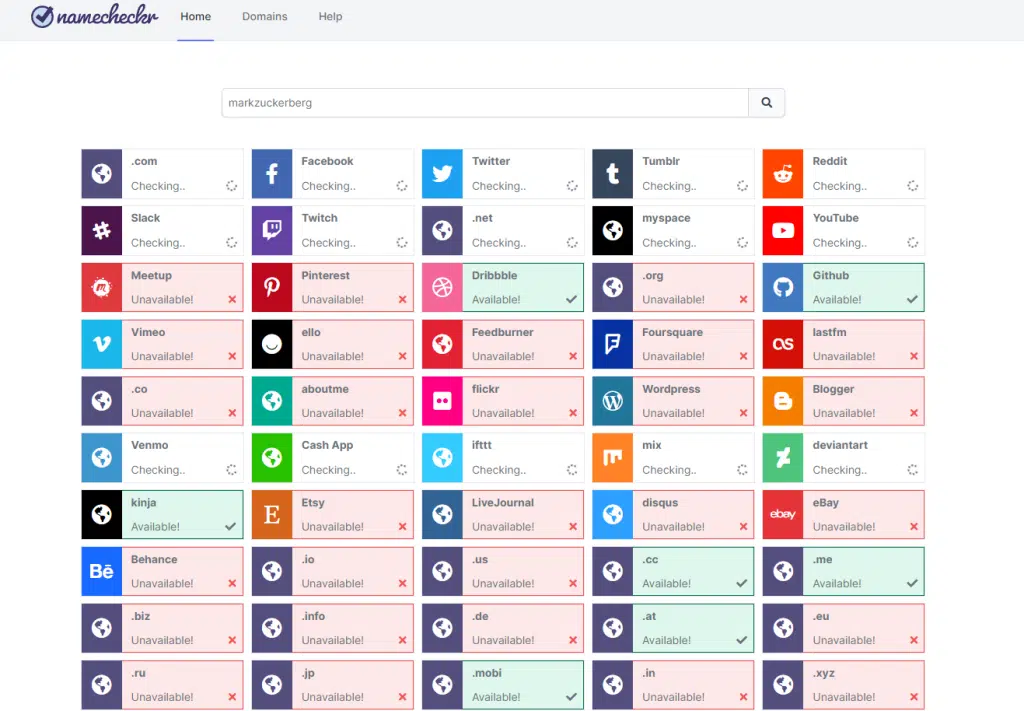
7. Now in the username search engine category we will see many tools available to search usernames for many databases. so here we will go with the namecheckr tool for searching the details about (Mark Zuckerberg).
8. after opening the tool website then enter the desired username and click on the search button, and it will show the result in green color where that username is registered on which website.
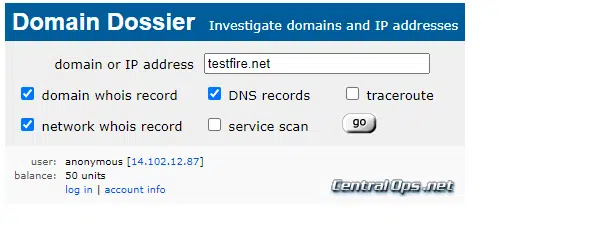
9. let’s tool for footprinting this time our target will be a website, and we need to find the Whois record of that website so for this we will go with the domain name category and then the Whois record sub-category, and from the tool list, we will choose domain dossier tool.
10. After clicking on the Domain Dossier subcategory the tool website will appear on the screen. You need to enter the domain and choose what type of information you want from the tool of that domain or IP address.
11. after clicking on the go button your query will be executed, and you see the result on the screen and that information will be enough for understanding the domain nature and network nature of that organization.
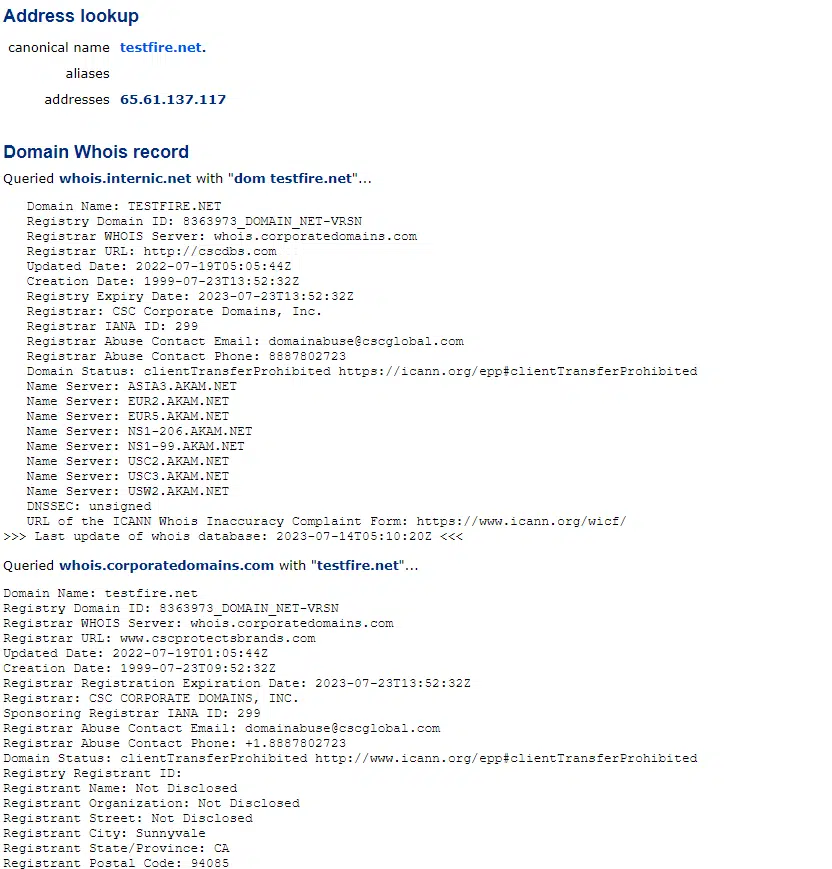
these are the basic example of how you can use this OSINT framework for footprinting the target. kindly practice and explore more tools and services in this framework. This framework is a bundle of all the services and tools available for open-source intelligence information gathering.
You will find every tool over here for information gathering of a target which can be an organization, person, website, domain, IP address, etc.